The latest research in cancer
Cancer disrupts lives, killing more than seven million people worldwide and half a million in the United States each year. To tackle this complex disease, the Biodesign Institute takes a comprehensive approach to cancer research — from diagnosis and treatment to prevention — as well as a collaborative approach that unites clinicians and researchers of different expertise.
Frequently asked questions
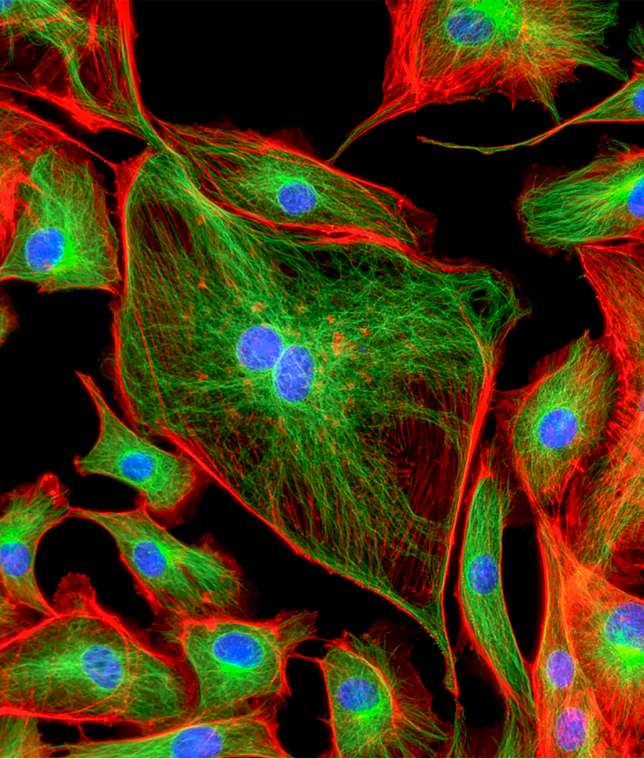
The definition of cancer is a group of diseases caused by abnormal cells dividing without control. These cells can invade nearby tissues and also spread to other parts of the body through the bloodstream and lymphatic system.
The Greek physician Hippocrates, known as the “father of medicine,” used the term karkinos, which means “crab,” to describe tumors. There are several theories why he chose this name: the hard texture of tumors reminded him of a crab shell, a tumor and its finger-like projections looked like a crab’s body, the pain of a tumor was like being pinched by a crab, or the difficulty in getting rid of a tumor was similar to a crab refusing to let go. Later, the Roman physician Celsus translated the term into the Latin word for crab, which is cancer.
Cancers are named after the area where they start (even if they move to other areas) and the type of cell they’re made of. The top five most common cancer types are breast cancer, lung cancer, prostate cancer, colorectal cancer and melanoma skin cancer. There are also medical terms for the general types of cancer: carcinoma, which is cancer of the skin or tissues that line other organs; sarcoma, which is cancer of connective tissues like blood vessels and muscle; leukemia, which is cancer of the bone marrow; lymphoma, which is cancer of the lymphatic system; and myeloma, which is cancer of specific white blood cells called plasma cells.
Our experts are researching over two dozen cancers, including:
- Blood cancer.
- Bone cancer.
- Brain cancer.
- Breast cancer.
- Colon cancer.
- Colorectal cancer.
- Glioblastoma.
- HPV.
- Liver cancer.
- Lung cancer.
- Lymphoma.
- Melanoma.
- Multiple myeloma.
- Neuroblastoma.
- Oral cancer.
- Osteosarcoma.
- Ovarian cancer.
- Pancreatic cancer.
- Prostate cancer.
Mutations to cellular DNA cause cancer. A cell’s DNA has instructions about how to grow and divide; when there’s an error in those instructions, the cell could grow more rapidly, fail to stop uncontrolled growth or make mistakes when repairing DNA. Cancer can be genetic if you have a mutation you inherited from your parents, but this is only true in a small percentage of cases. Genes can also mutate due to outside forces, like smoking, radiation, chronic inflammation, hormones or lack of exercise. Signs of cancer are different depending on what area of the body is affected. Some general symptoms that can be associated with cancer include fatigue, a lump or thickened area under the skin, weight changes, trouble breathing, persistent indigestion, and persistent muscle or joint pain.
Today, there are many available ways to treat cancer; the type of cancer and the goal of treatment will determine which method or combination of methods is right for a patient. Doctors use surgery to remove as much of the cancer as possible. Chemotherapy uses medication to kill cancer cells. Radiation therapy uses energy beams like X-rays to kill cancer cells. The radiation can come from a machine or be placed inside the body. Immunotherapy boosts the immune system to attack cancer cells. Hormone therapy can help check the growth of certain types of cancer that are affected by hormones.
Efforts underway
A cancer blood test
Researchers at the institute have developed inexpensive technologies that could allow people to detect diseases, including cancer, before any symptoms appear — all with a drop of blood.
Using methods borrowed from computer chip production, scientists make slivers of proteins on the surface of a silicon wafer to read antibody profiles. This creates an immunosignature which shows early signs of disease in the body.
18
Types of cancer studied at Biodesign.
Personalized cancer treatment
In the 21st century, molecular medicine is teaching us that what was once simply one type of cancer, like breast cancer, should now be recognized as more than a half dozen different diseases. Each responds differently to a given therapy and carries a different prognosis.
Personalized medicine relies on diagnostic tests to identify patients’ specific diseases as well as new therapeutics that are tailored to each disease. This not only brings cancer patients the best treatment options for them, it also reduces the negative side effects, costs and time that come with ineffective therapies.
Researchers at the Biodesign Institute are studying cancer immunotherapy as well as other biologically based treatments, like using viruses, bacteria or nanorobots made of DNA to target tumors. Our scientists are also exploring the roles of proteins and their dysfunction in disease, knowledge which can help develop more personalized treatments.
A vaccine for cancer
The Biodesign Institute is collaborating with Mayo Clinic in Arizona to eradicate cancer by developing therapeutic and even preventative vaccines against cancer. These vaccines take advantage of the immune system’s ability to recognize proteins created by cancers.
The first target we are exploring is breast cancer. The idea is that if we could immunize a person with a collection of proteins that mimic those of a breast tumor, the immune system would learn to recognize those proteins and arm itself against breast cancer. If the platform technology is successful, it could be applied to other cancers as well.
To prevent almost all forms of cancer in dogs, our researchers are conducting a clinical dog trial of a near-universal, preventative cancer vaccine. The hope is that, if effective, we can develop such a vaccine for human use and make cancer a disease of the past.
A “Living Drug” that Beats Cancer | ASU KEDtalks® featuring Karen Anderson
Latest news on cancer
Related experts
Related centers

Virginia G. Piper Center for Personalized Diagnostics

Center for Applied Structural Discovery
Related facilities
Studying cancer requires specialized equipment. These facilities support this work.
Advance our efforts
Support cancer research by making a donation.